Encrypted Storage, Made Easy.
When your web app is handling sensitive information — be it API credentials, database passwords, or sensitive personal data — it’s important to keep it protected. It certainly shouldn’t be sitting in your source code, for anyone to see. It should be kept encrypted, until the time it’s needed. This is called encryption at rest.
With Anvil, you can store password or API keys encrypted in your app, with a name – for example, I could store my GitHub password in a secret called github_password. Then I can use it in my app, like this:
username = "meredydd"
password = anvil.secrets.get_secret("github_password")
r = anvil.http.request("https://api.github.com/user/repos", json=True,
username=username, password=password)I can also create and store an encryption key, and use it to encrypt and decrypt data. Encrypted-at-rest data storage is this simple:
# This app has an encryption key named 'my_key':
@anvil.server.callable
def save_secret_data(new_text):
encrypted_text = anvil.secrets.encrypt_with_key('my_key', new_text)
app_tables.secret_data.add_row(text=encrypted_text)Watch our video tutorial here, or read our API documentation :
Note: This guide includes screenshots of the Classic Editor. Since we created this guide, we've released the new Anvil Editor, which is more powerful and easier to use.
All the code in this guide will work, but the Anvil Editor will look a little different to the screenshots you see here!
How it works
App Secrets are encrypted, and stored with the source code for your Anvil app. Secrets and keys are encrypted with a key unique to that application – making the encrypted value useless outside that app.
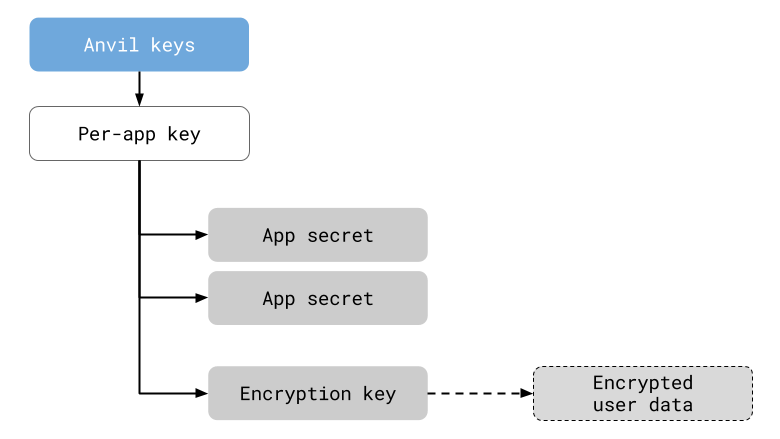
All encryption is performed with AES-GCM, a high quality, industry-standard encryption scheme that avoids the pitfalls of using low-level cryptographic libraries. For more details, see our documentation .
We believe security and privacy are important, and we are proud to empower our users to use cryptography easily and safely. We are grateful to the security and privacy researchers who have helped us develop and validate this feature, and we welcome contact from the security community at security@anvil.works.
 By
By