Using your own Azure Active Directory
You can limit your app to users within a particular Azure Active Directory. This is useful if your organization uses Azure Active Directory to manage its user accounts - your Anvil apps will be limited to only users within your organization.
Configuration
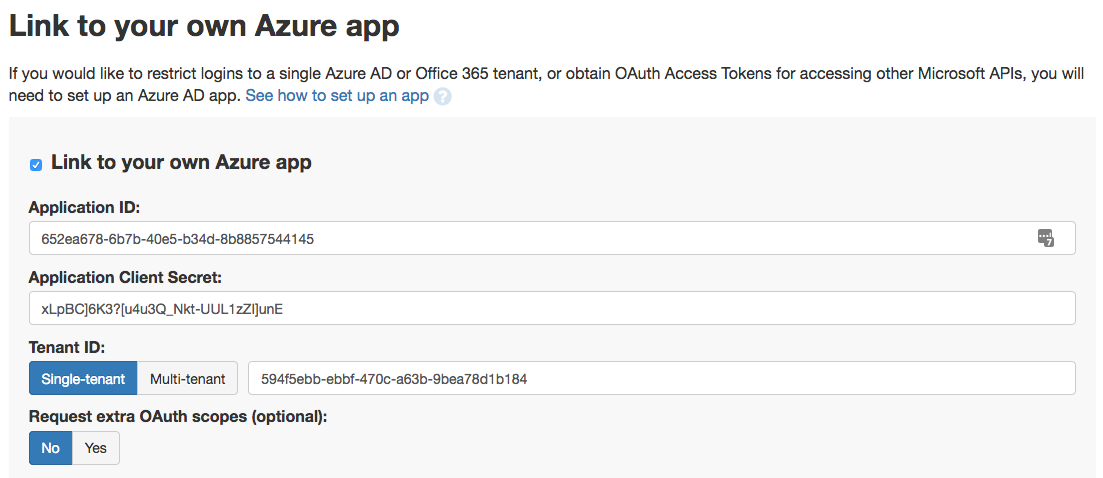
You must point Anvil to your Azure Active Directory by setting an App Registration up in Azure and pasting the relevant IDs into Anvil. This only takes a few minutes - follow this guide to see how.
Presenting a login form
To present users with a login form, run this function call in your client-side code:
anvil.microsoft.auth.login()This is the same function call you use for global Microsoft Single-Sign-On. The difference is that when the ‘Link to your own Azure app’ box is checked and ‘Single-tenant’ is selected, you are restricting access to within your own Azure Active Directory.
User authorization
To check if a user is logged in, run this function call in your client or server-side code:
email = anvil.microsoft.auth.get_user_email()If the user has logged in successfully, this returns the email address they logged in with. It returns None if
the user dismissed the login form.
You can check for None in order to restrict part or all of your app to logged-in users:
if anvil.microsoft.auth.get_user_email() is not None:
self.do_what_the_app_does()If you want to restrict access to particular users, you can check the email address of the logged-in user. Imagine you
have a Data Table called user_roles with email and role columns. Such a table maps user email addresses to
roles that give them certain privileges. You could use it to control who can do what in your app using an if statement
like this:
user_role = app_tables.user_roles.get(
email=anvil.microsoft.auth.get_user_email()
)
if user_role['role'] == 'admin':
self.show_admin_view()
else:
self.show_standard_view()Next up
Once you’ve got Anvil linked to your Azure account, you can also access the many Microsoft APIs
using anvil.http.request from client or server code.
Do you still have questions?
Our Community Forum is full of helpful information and Anvil experts.
